Security Policies In Information Security What is tokenization In data security tokenization is the process of converting sensitive data into a nonsensitive digital replacement called a token that maps back to the original Tokenization can help protect sensitive information For example sensitive data can be mapped to a token and placed in a digital vault for secure storage
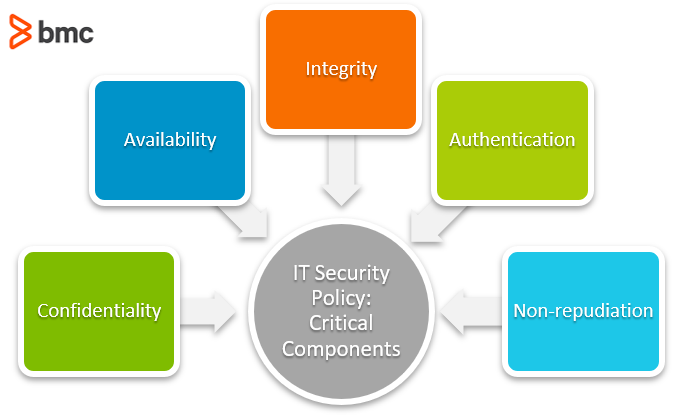
IT security protects an organization s computer systems networks an digital data from unauthorized access data breaches cyberattacks and other malicious activity La seguridad inform tica protege los sistemas inform ticos las redes y los datos digitales de una organizaci n contra el acceso no autorizado las filtraciones de datos los ataques cibern ticos y otras actividades maliciosas
Security Policies In Information Security
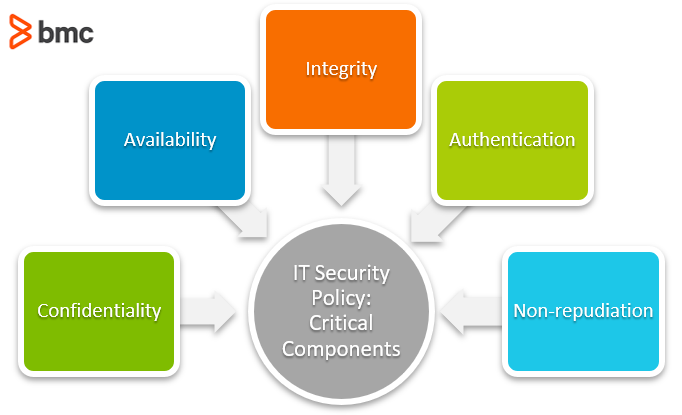
Security Policies In Information Security
https://s7280.pcdn.co/wp-content/uploads/2021/02/key-30.png
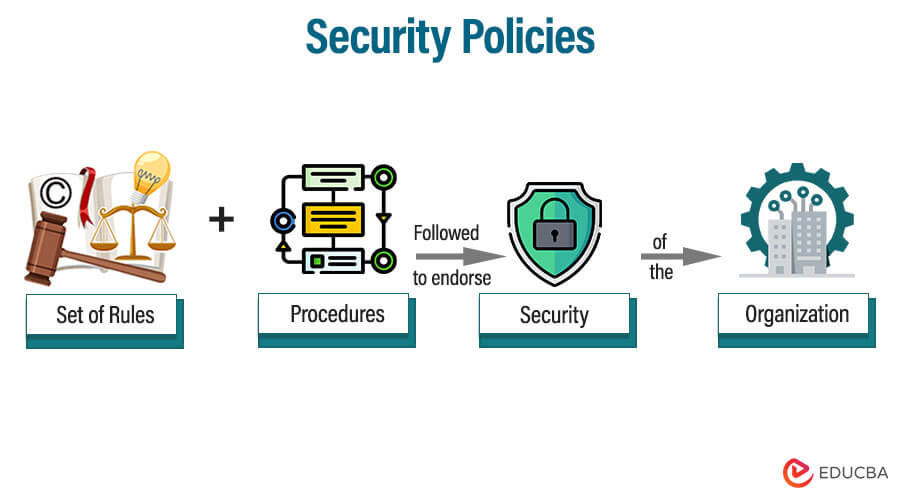
Security Policies List Of 6 Most Useful Security Policies
https://cdn.educba.com/academy/wp-content/uploads/2019/12/Security-Policies-1.jpg
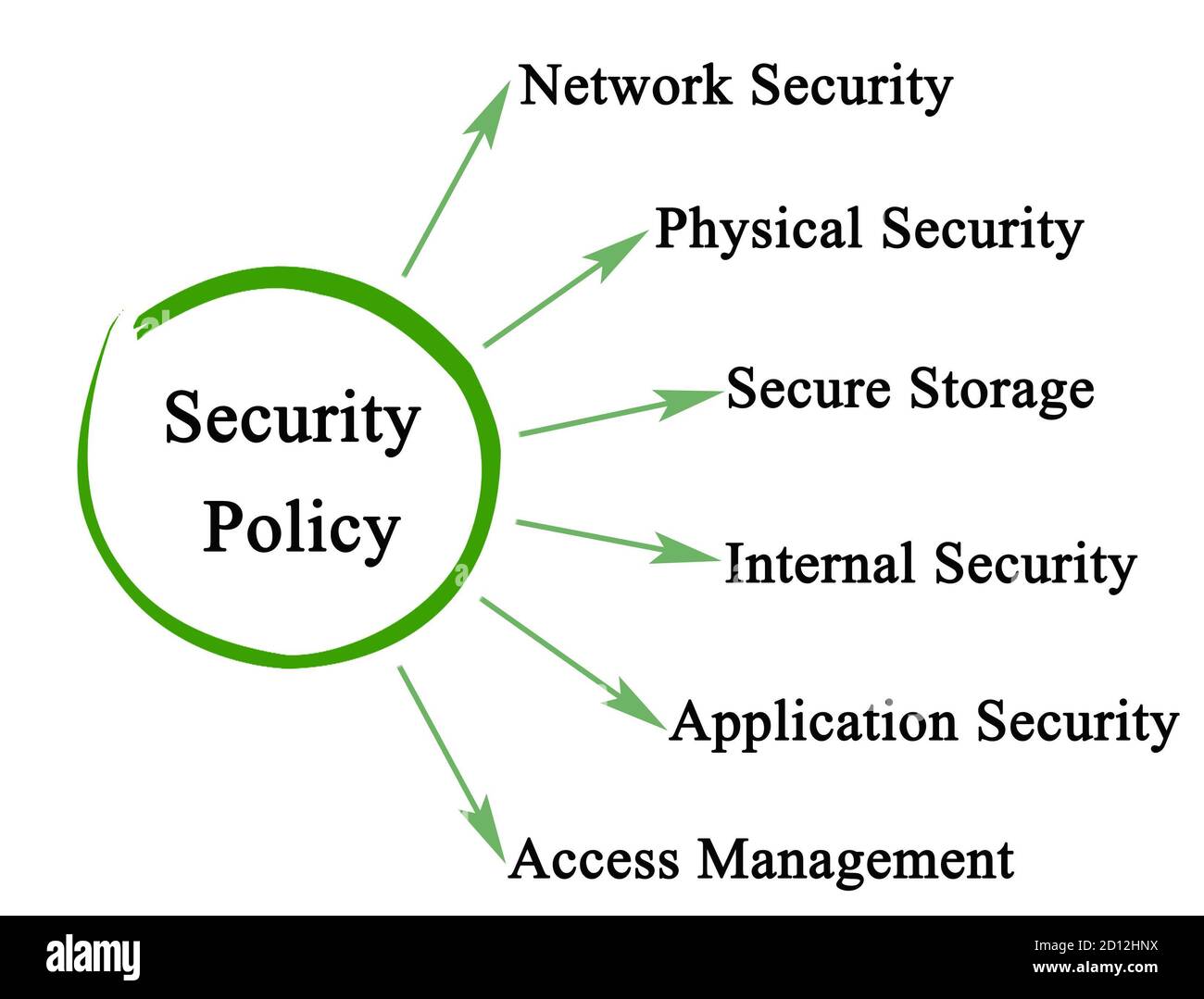
Six Types Of Security Policy Stock Photo Alamy
https://c8.alamy.com/comp/2D12HNX/six-types-of-security-policy-2D12HNX.jpg
Information security InfoSec is the protection of important information against unauthorized access disclosure use alteration or disruption API security is a set of practices and procedures that protect application programming interfaces APIs and the data they transmit from misuse malicious bot attacks and other cybersecurity threats
Most of us think of cybersecurity as a purely digital affair but cyberattacks can actually begin right here in the physical world Don t want to fork over 30 for a one year subscription to Windows 10 Extended Security Updates Microsoft is offering a couple of ways to avoid the fee But there is a catch
More picture related to Security Policies In Information Security
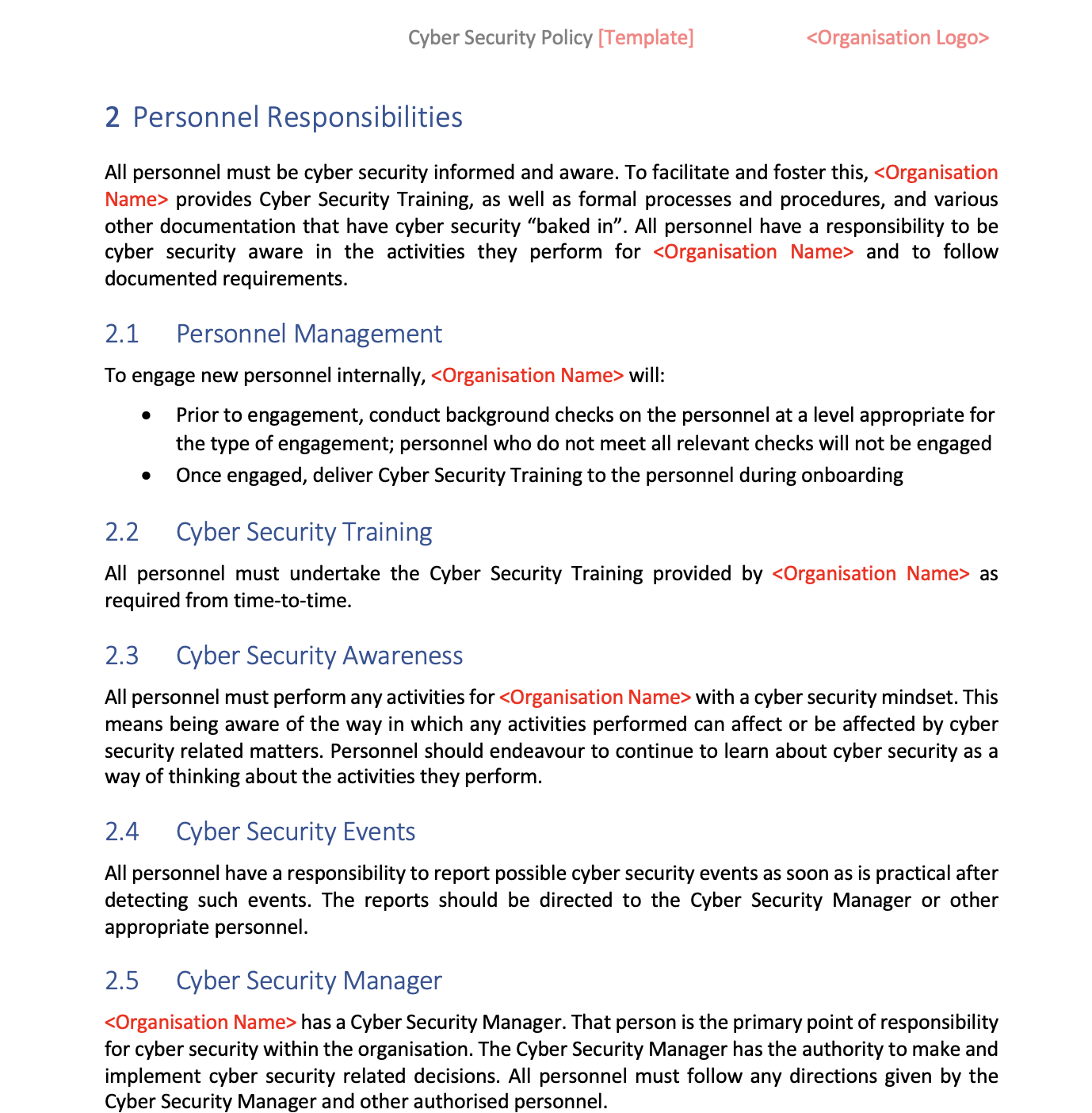
Policy Template Examples
https://helpdesk.realworld.net.au/hc/article_attachments/4409253765913/Screen_Shot_2021-11-10_at_4.25.03_pm.png
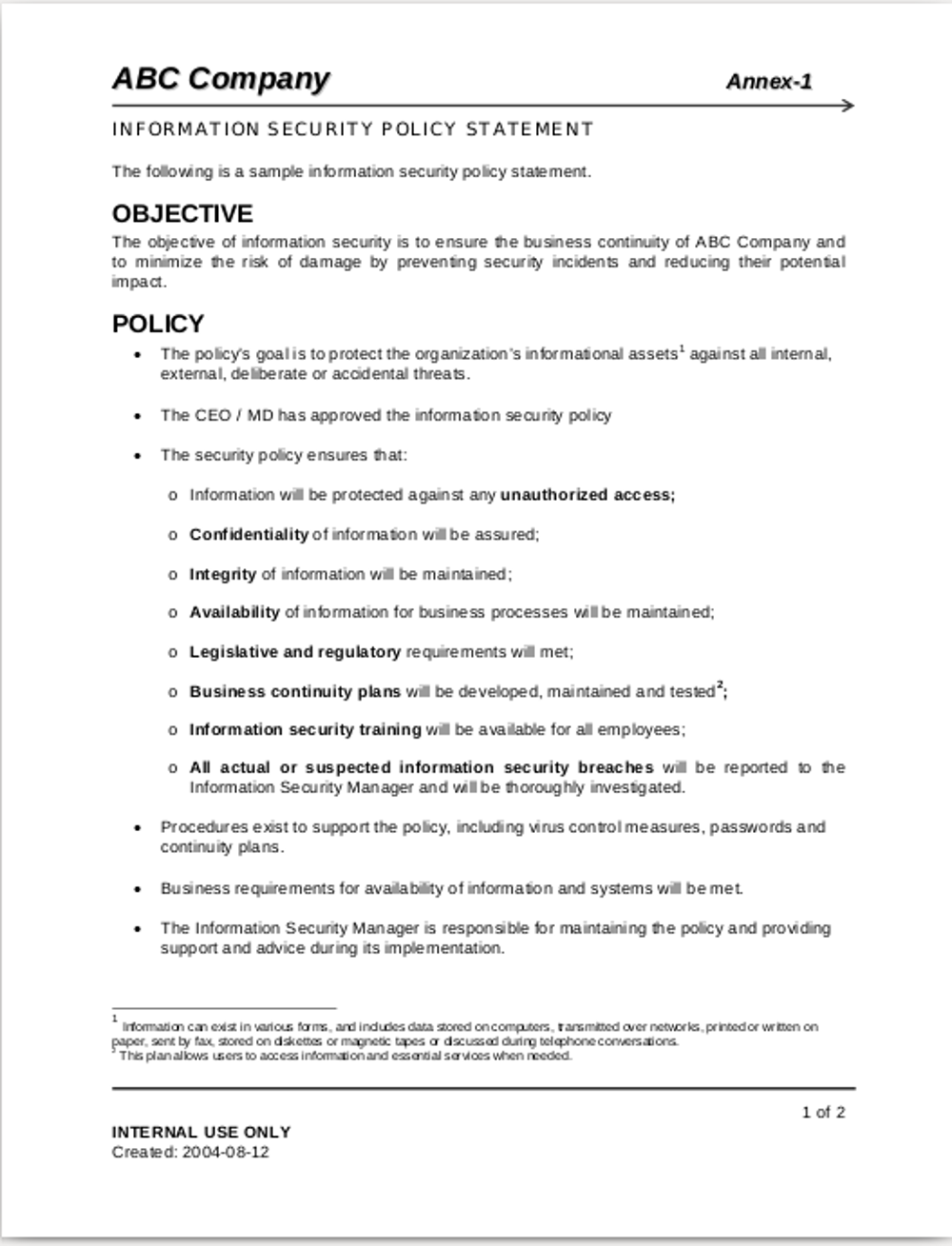
Organizational Security Policy
https://images.examples.com/wp-content/uploads/2017/10/71.png
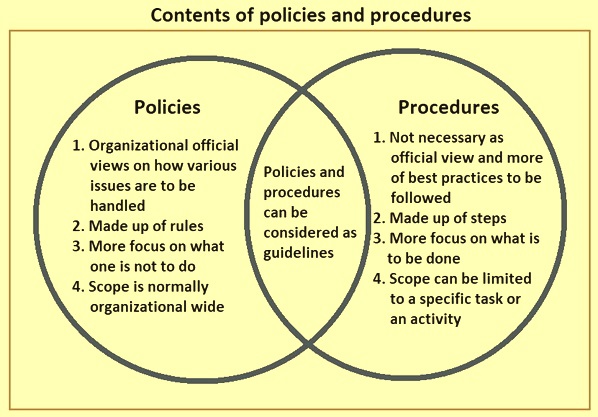
Policies And Procedures Australian Medical Association
https://www.ama.com.au/sites/default/files/inline-images/Contents-of-policies-and-procedures.jpg
DevOps security or DevSecOps is a developmental approach where security processes are prioritized and executed during each stage of the software development lifecycle SDLC ZDNET news and advice keep professionals prepared to embrace innovation and ready to build a better future
[desc-10] [desc-11]
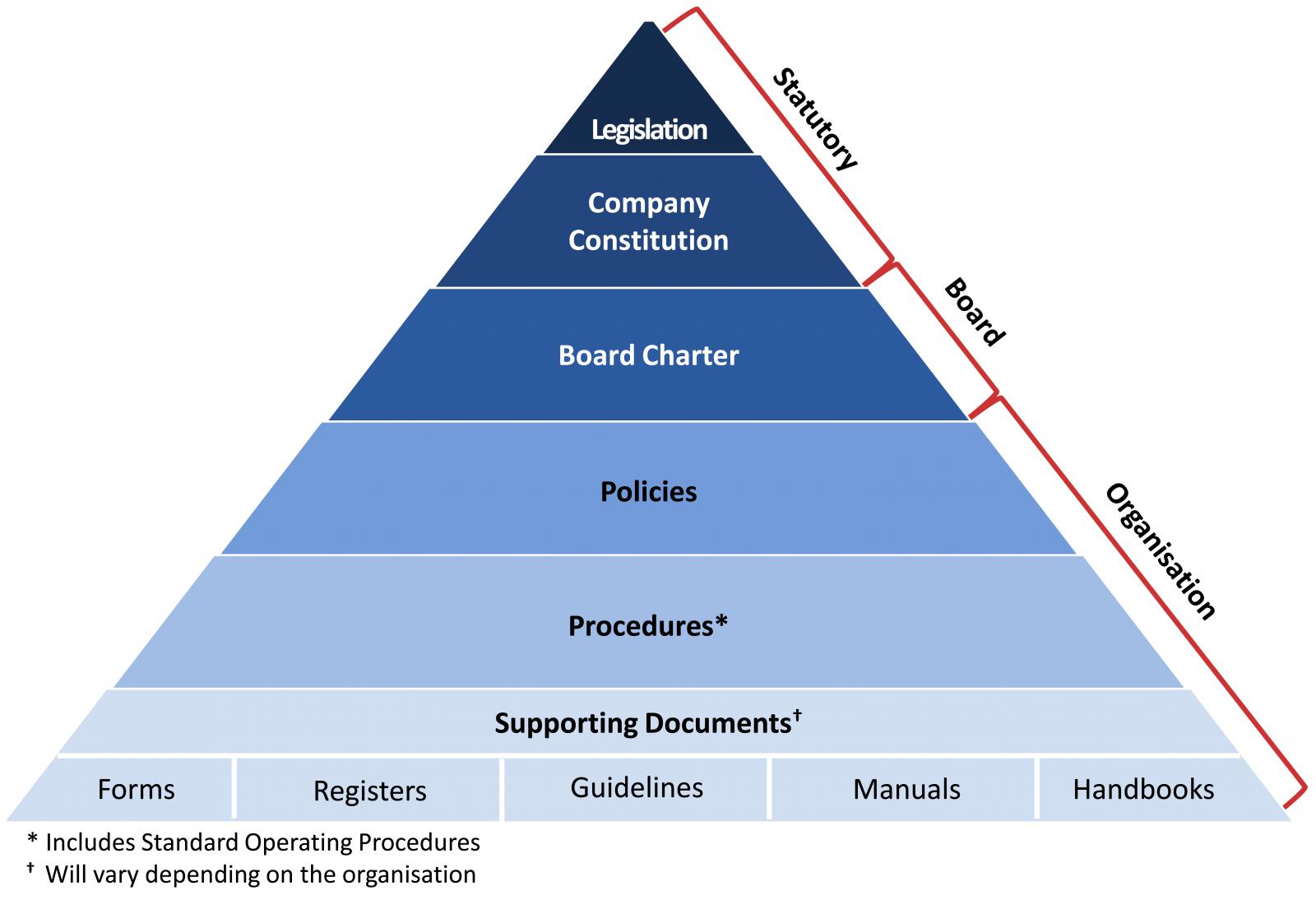
Data Governance Policy Template Prntbl concejomunicipaldechinu gov co
https://www.effectivegovernance.com.au/content/Document/News Uploads/Policy on Policies - Policy framework.jpg
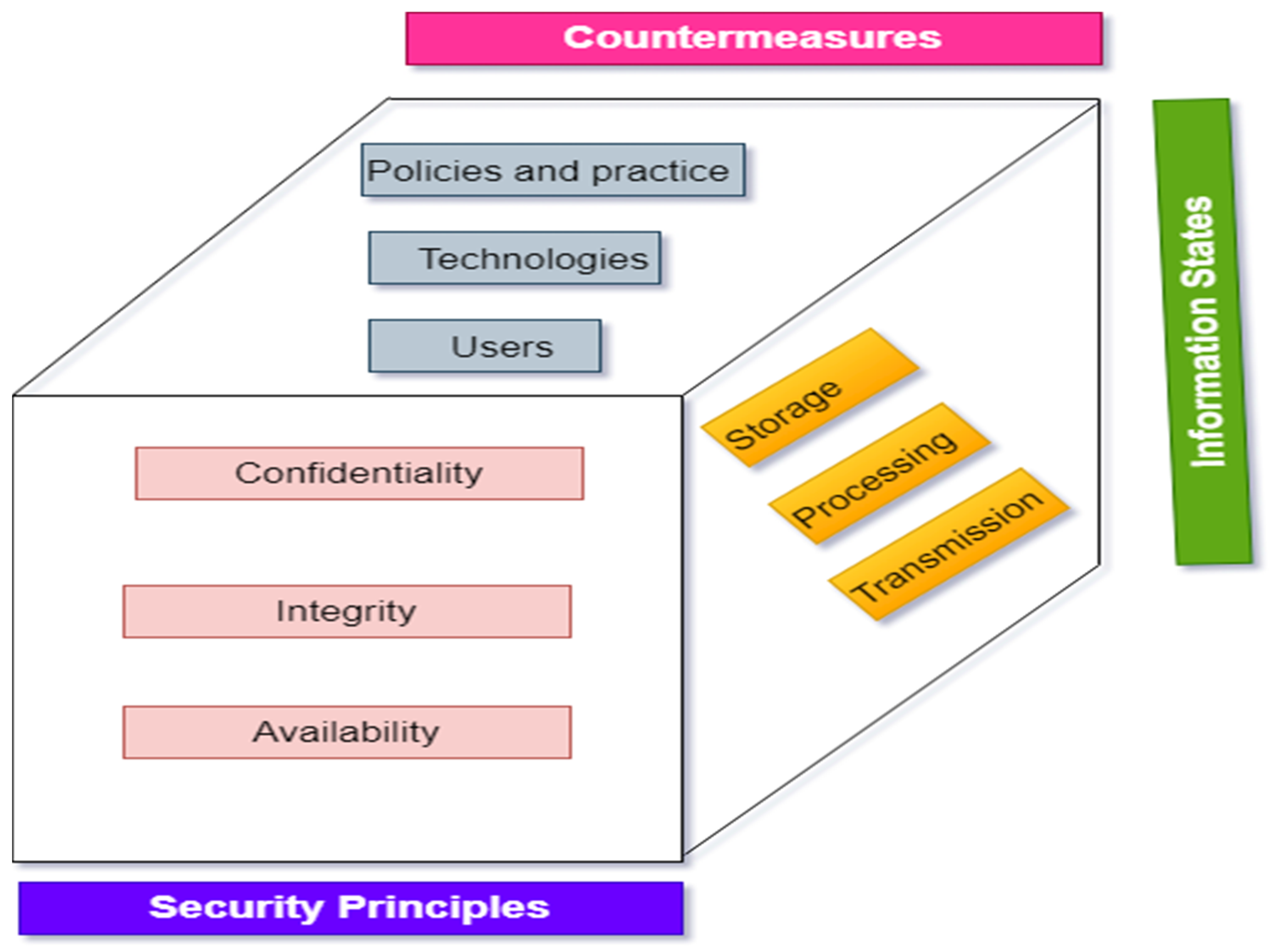
25 Simplicity Pattern 1035 SaharaNusa
https://www.mdpi.com/electronics/electronics-12-01333/article_deploy/html/images/electronics-12-01333-g001.png
https://www.ibm.com › think › topics › tokenization
What is tokenization In data security tokenization is the process of converting sensitive data into a nonsensitive digital replacement called a token that maps back to the original Tokenization can help protect sensitive information For example sensitive data can be mapped to a token and placed in a digital vault for secure storage
https://www.ibm.com › think › topics › it-security
IT security protects an organization s computer systems networks an digital data from unauthorized access data breaches cyberattacks and other malicious activity
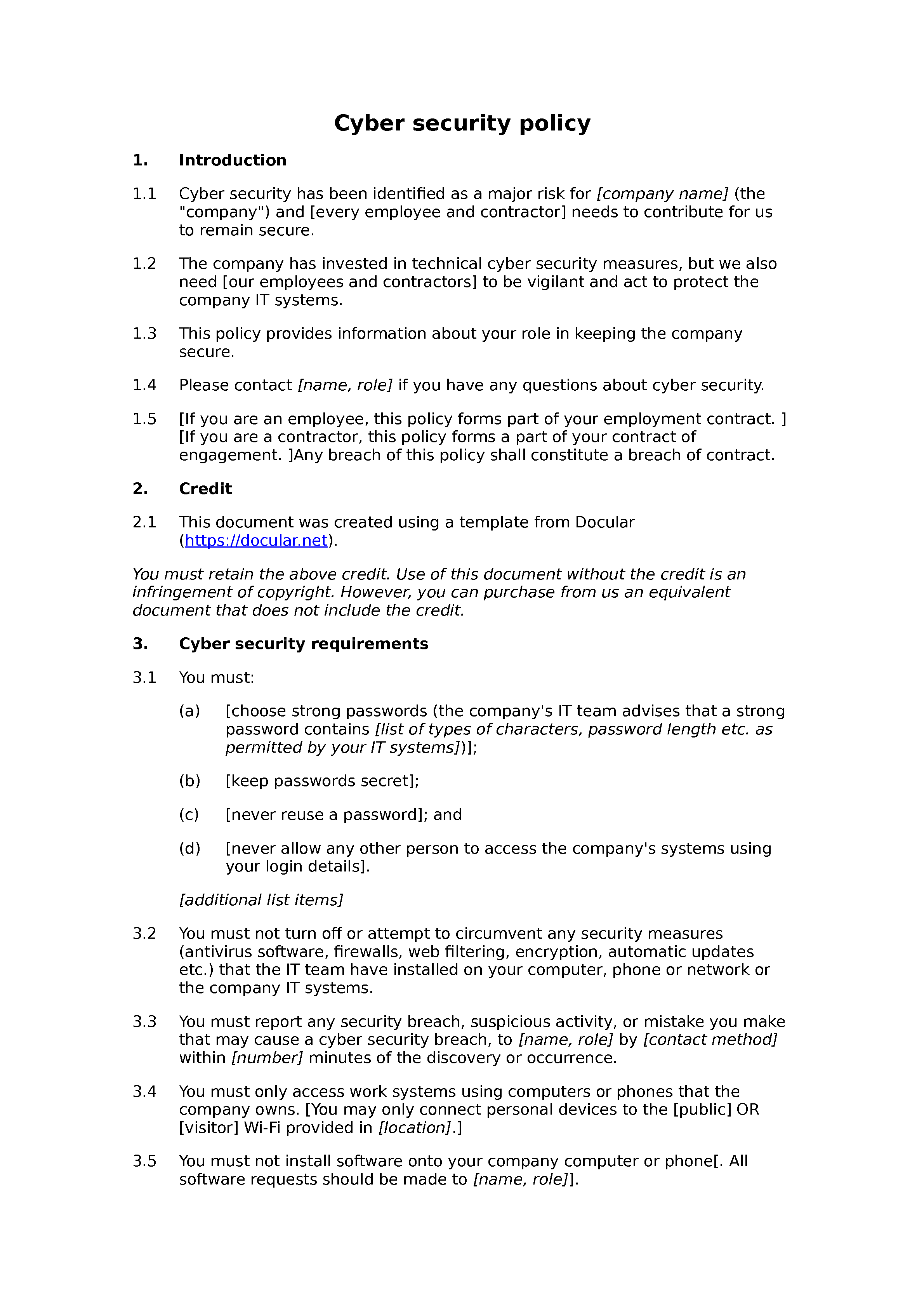
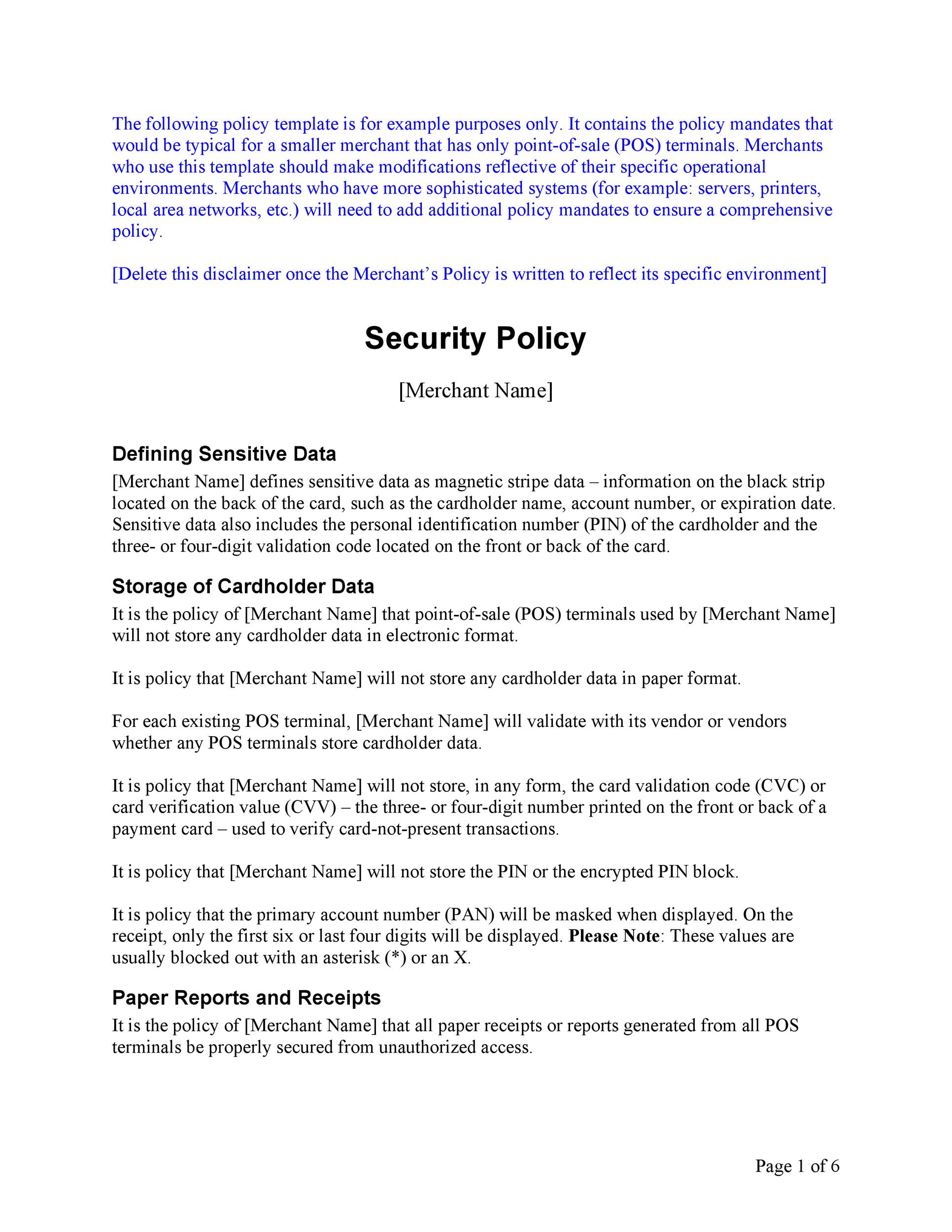
Free Cyber Security Policy Docular
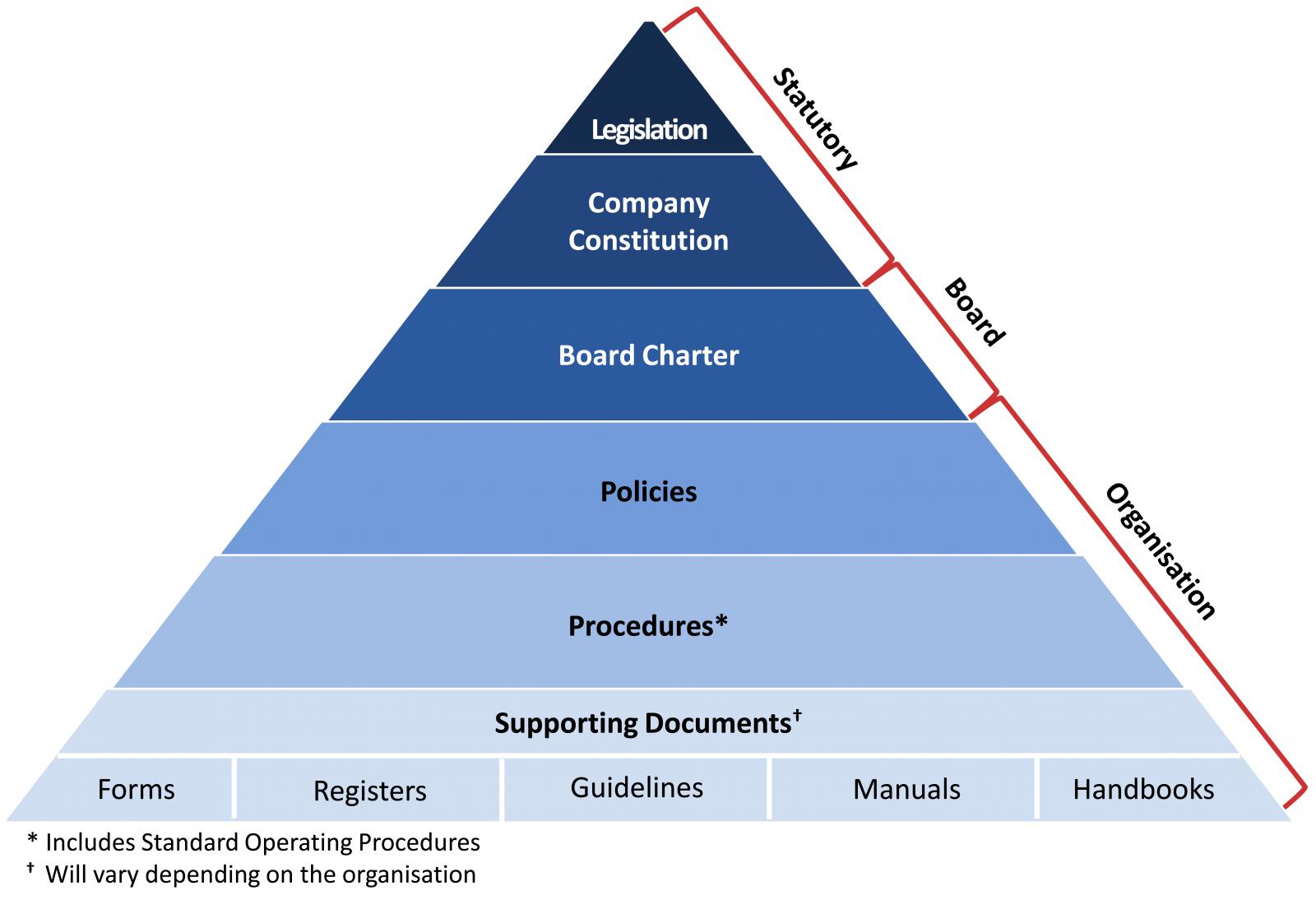
Data Governance Policy Template Prntbl concejomunicipaldechinu gov co
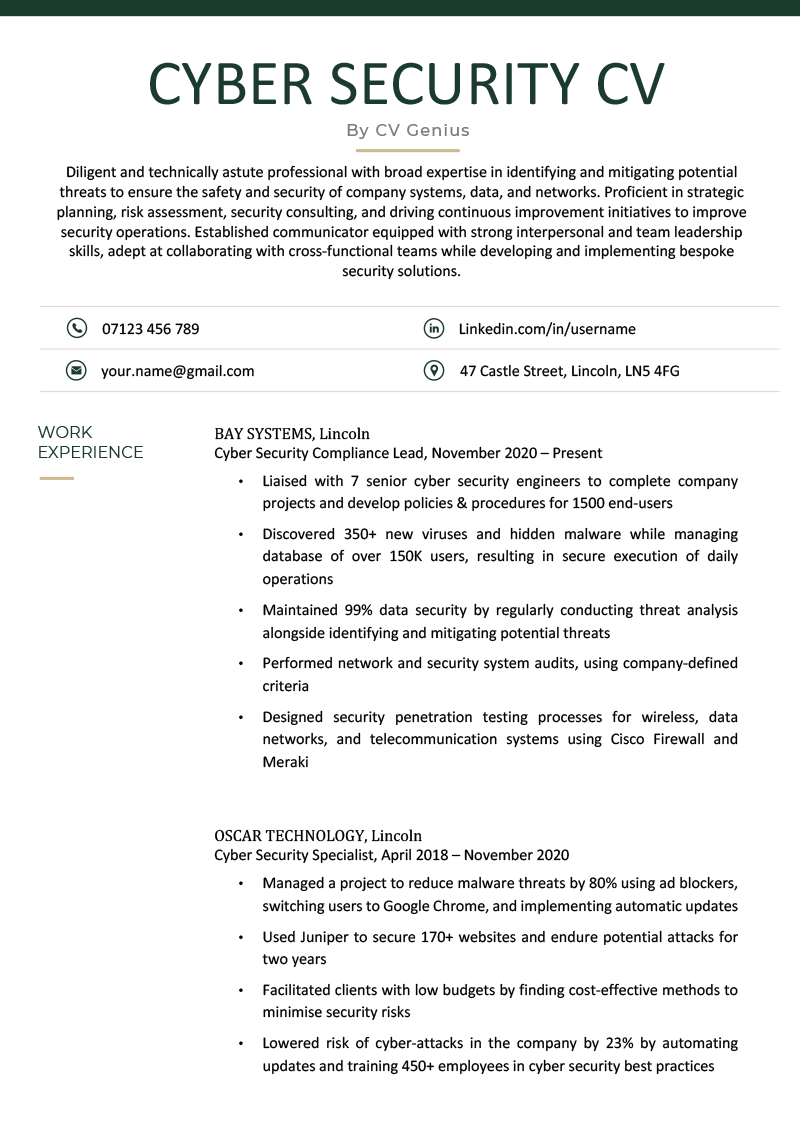
Cyber Security CV Free Example Template Guide
Isms Policy Template Prntbl concejomunicipaldechinu gov co

Information Technology Security Management
Cybersecurity Plan Template
Cybersecurity Plan Template

Policies And Procedures Images
What Is Information Policy And How To Create One Sprinto

How Enterprise Cybersecurity Protects Your Business
Security Policies In Information Security - Don t want to fork over 30 for a one year subscription to Windows 10 Extended Security Updates Microsoft is offering a couple of ways to avoid the fee But there is a catch