What Are The Two Main Types Of Threats To Information Security With 2 Step Verification or two factor authentication you can add an extra layer of security to your account in case your password is stolen After you set up 2 Step Verification you can
Starting August 31 2025 New apps and app updates must target Android 15 API level 35 or higher to be submitted to Google Play except for Wear OS Android Automotive OS and steam It Takes Two It Takes Two Hazelight
What Are The Two Main Types Of Threats To Information Security
What Are The Two Main Types Of Threats To Information Security
https://sites.wp.odu.edu/damianrichardson/wp-content/uploads/sites/32732/2024/04/top-5-cybersecurity-threats-c-level-executives.png

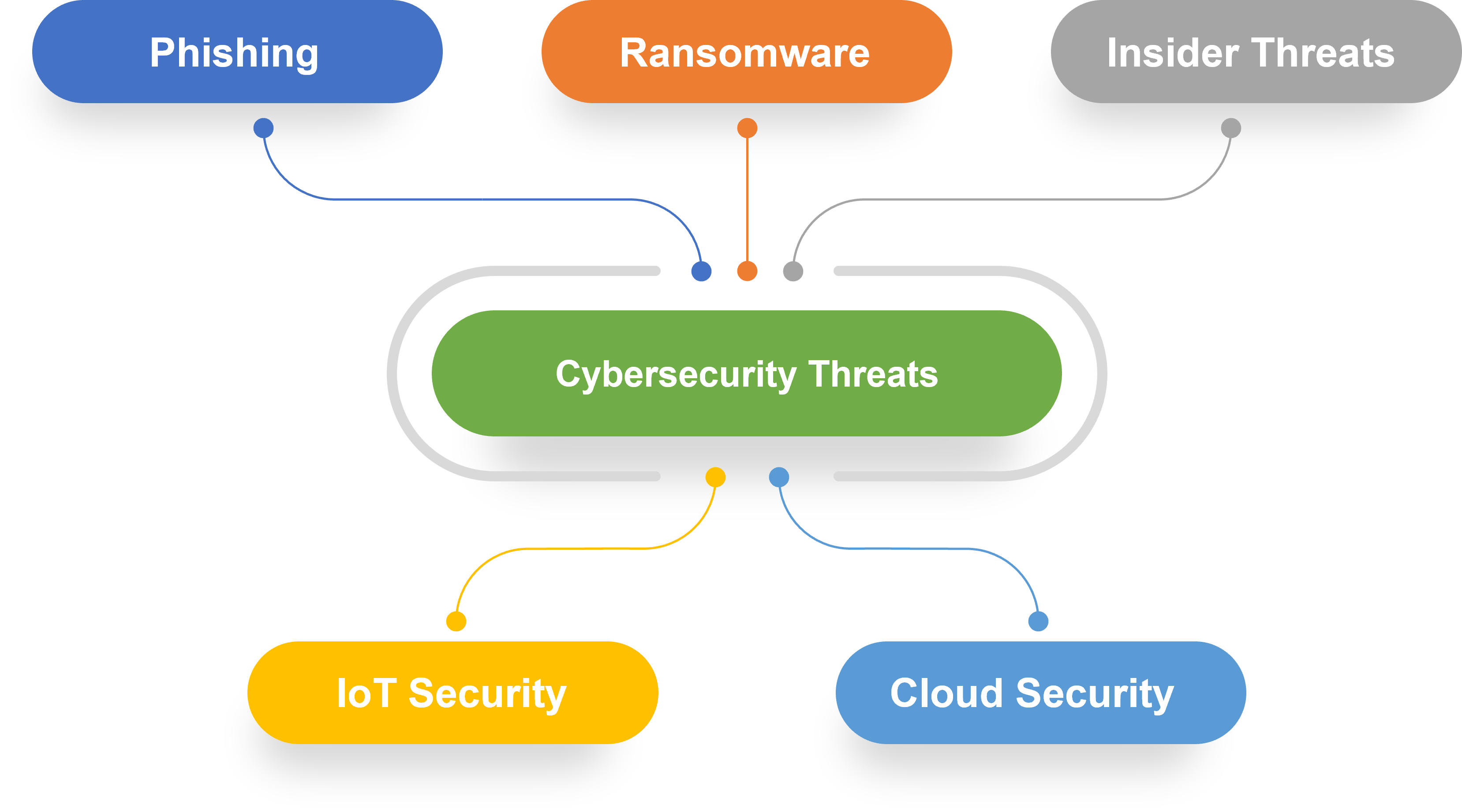
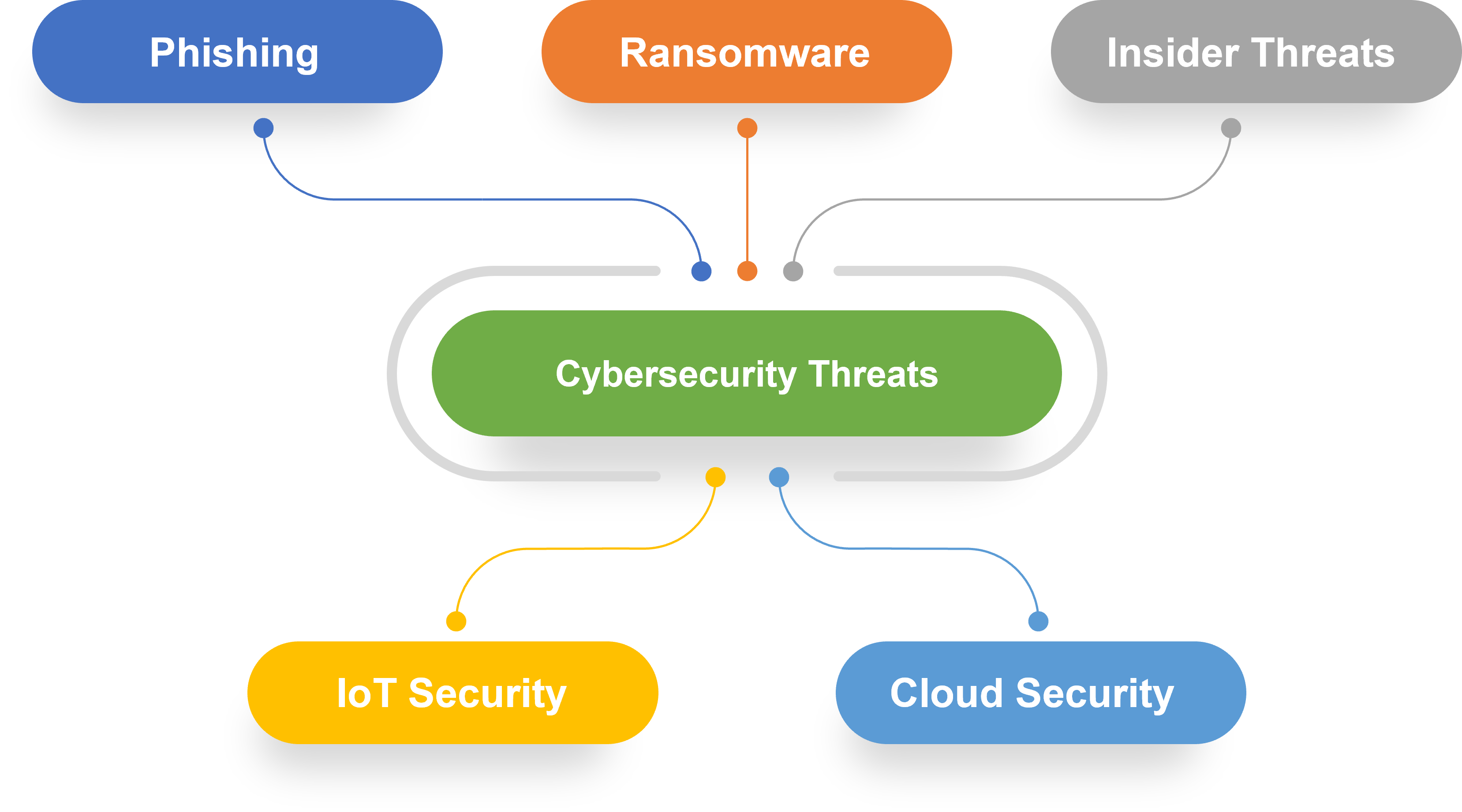
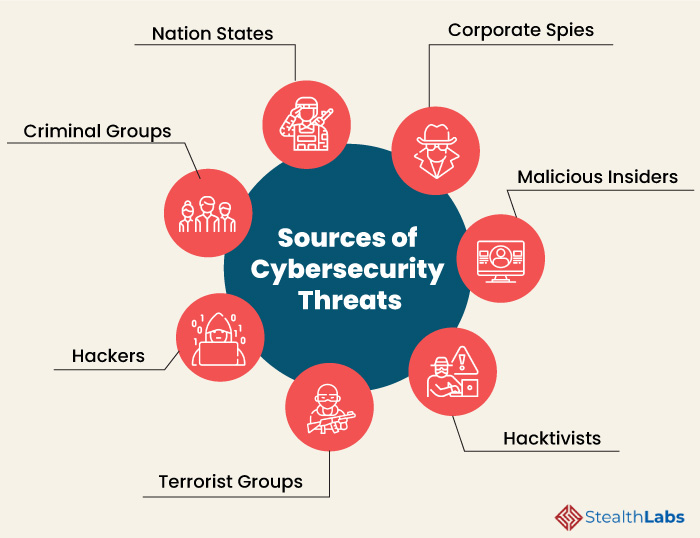
Threats
https://www.theamegroup.com/wp-content/uploads/2017/08/network-security-threats.jpg

Keylogging Concept Icon Cartoon Vector CartoonDealer 235356237
https://thumbs.dreamstime.com/z/ten-main-threats-cybersecurity-ten-cybersecurity-threats-169533058.jpg
Add line 1 Address line2 Address line1 If you ve lost access to your primary phone you can verify it s you with Another phone number you ve added in the 2 Step Verification section of your Google Account A hardware security
The Google Authenticator app can generate one time verification codes for sites and apps that support Authenticator app 2 Step Verification If you set up 2 Step Verification you can use If there are multiple businesses at the same address they can each have their own Business Profiles if they re Distinct businesses with different names and clearly visible differences in
More picture related to What Are The Two Main Types Of Threats To Information Security
Cyber Threats
https://www.dailyinfographic.com/wp-content/uploads/2020/07/Cyber-threats.jpg

Cyber Threats
https://d2ds8yldqp7gxv.cloudfront.net/Blog+Explanatory+Images/Top+Cybersecurity+Threats+1.webp

Web Security Threats Definition Types And Risks
https://securitygladiators.com/wp-content/uploads/threat-1024x819.jpg
2 Step Verification makes your account more secure If you turn off 2 Step Verification you remove an additional layer of security which can make it easier for someone else to access
[desc-10] [desc-11]

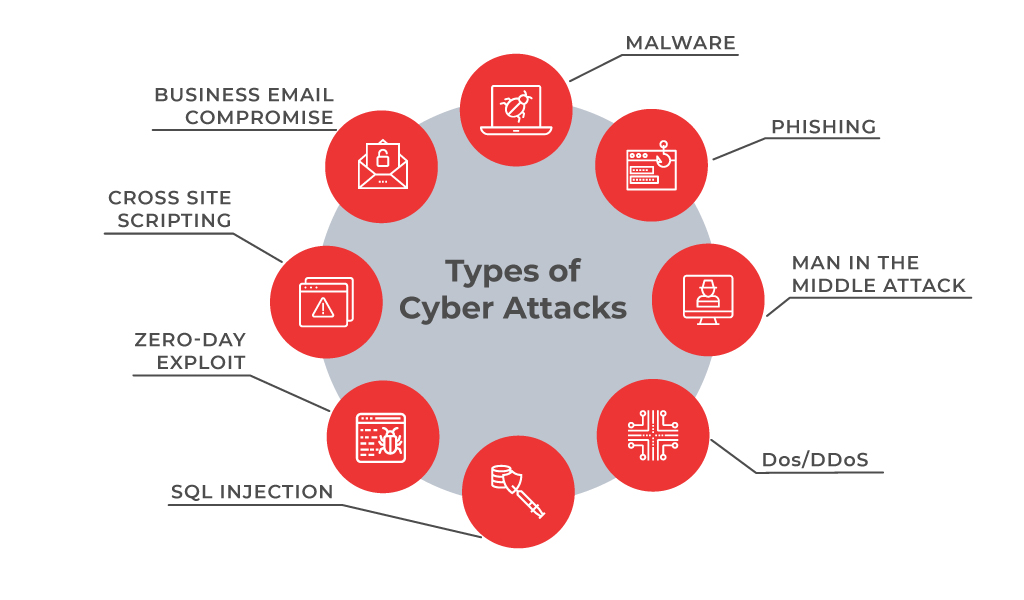
Cyber Attack Cheat Sheet Infographic
https://infographicjournal.com/wp-content/uploads/2020/04/types-of-cyberattacks-feat.jpg
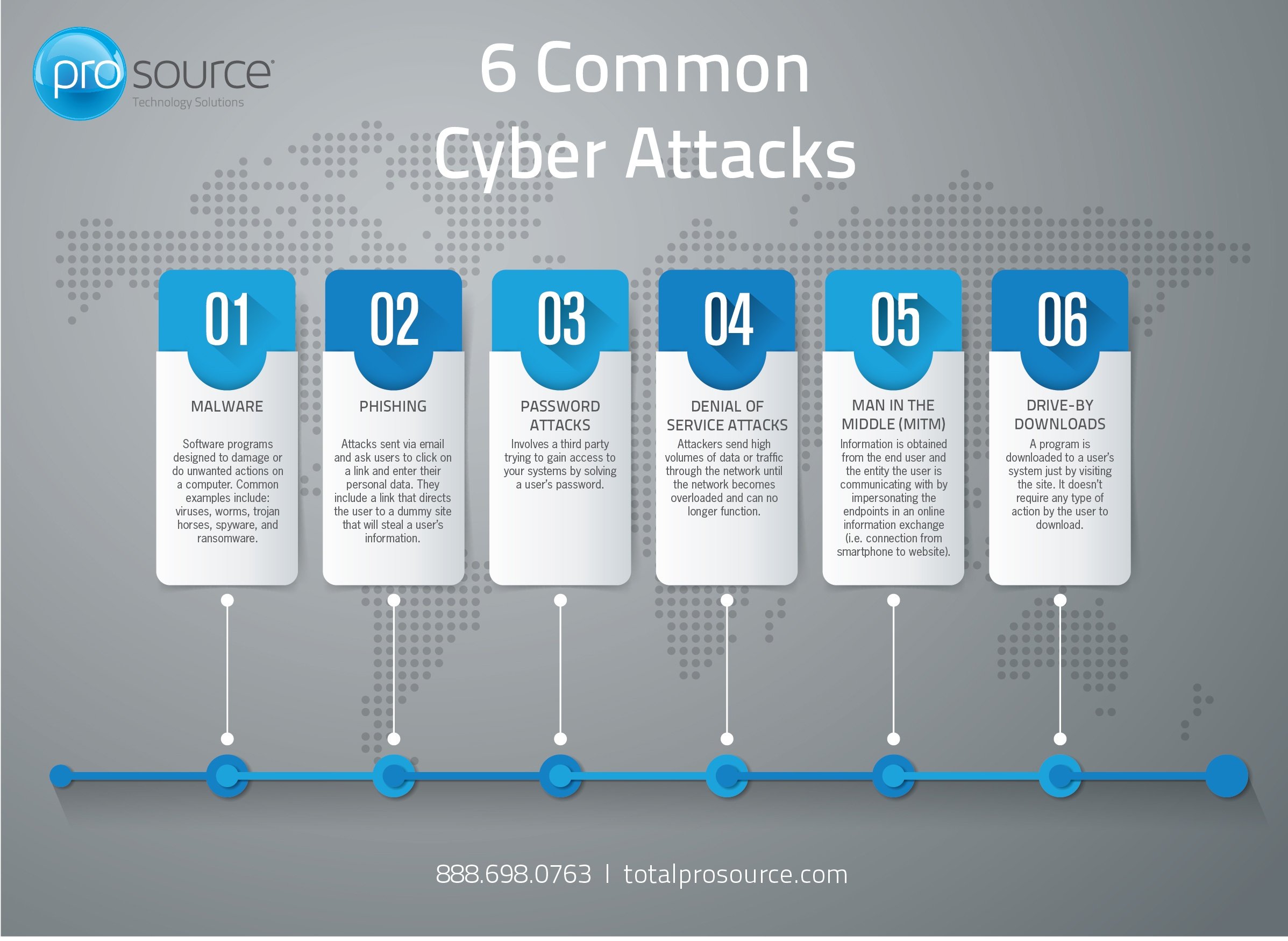
6 Common Types Of Cyber Attacks
https://cdn2.hubspot.net/hubfs/838527/6 Common Types of Cyber Attacks Infogrpahic.jpg
https://support.google.com › mail › answer
With 2 Step Verification or two factor authentication you can add an extra layer of security to your account in case your password is stolen After you set up 2 Step Verification you can

https://support.google.com › googleplay › android-developer › answer
Starting August 31 2025 New apps and app updates must target Android 15 API level 35 or higher to be submitted to Google Play except for Wear OS Android Automotive OS and
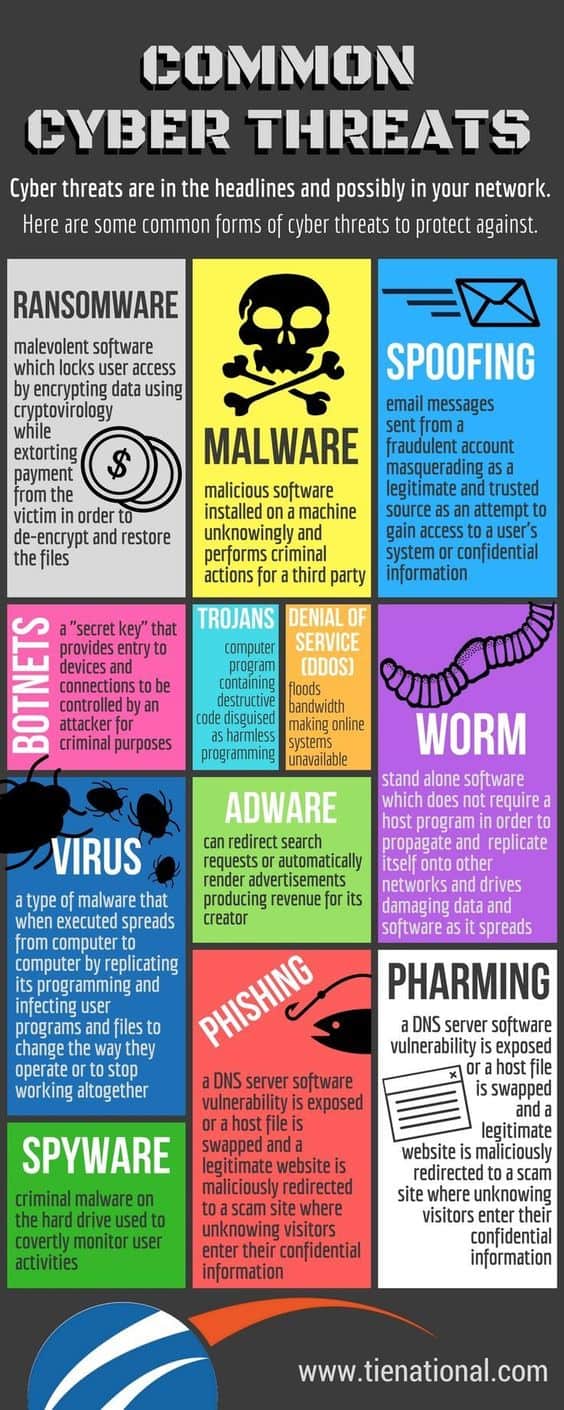
Computer Security Threats

Cyber Attack Cheat Sheet Infographic
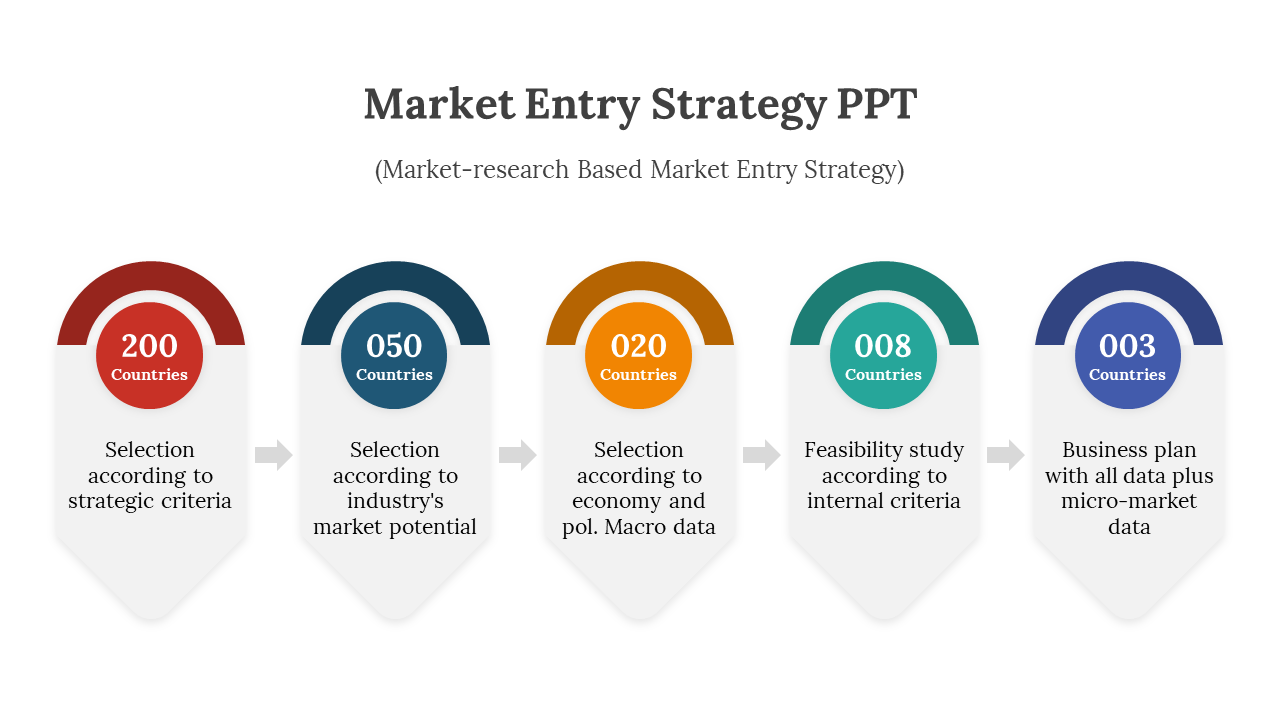
Market Entry Strategy PPT And Google Slides Themes
Things You Need To Know About Cyber Attacks Threats Risks Ecosystm
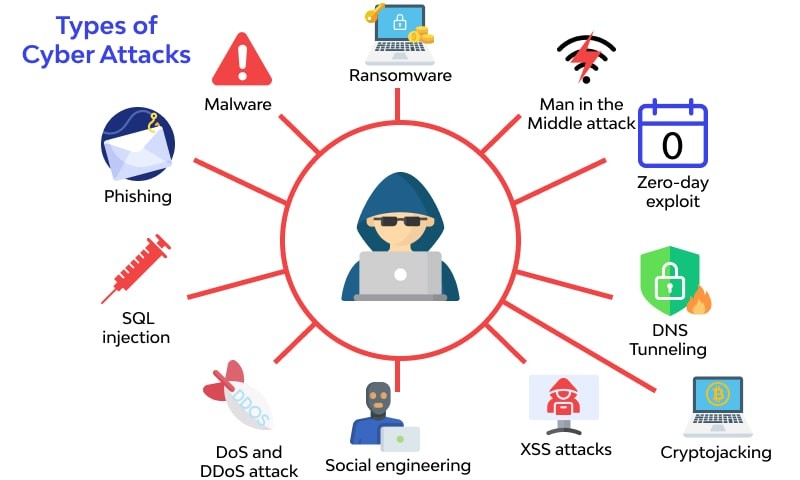
Cyber Security Attacks

1 Ecosystems pptx

1 Ecosystems pptx
Types Of Business Communication Training Ppt Presentation Graphics
Cyber Threats And Their Various Types Vrogue co
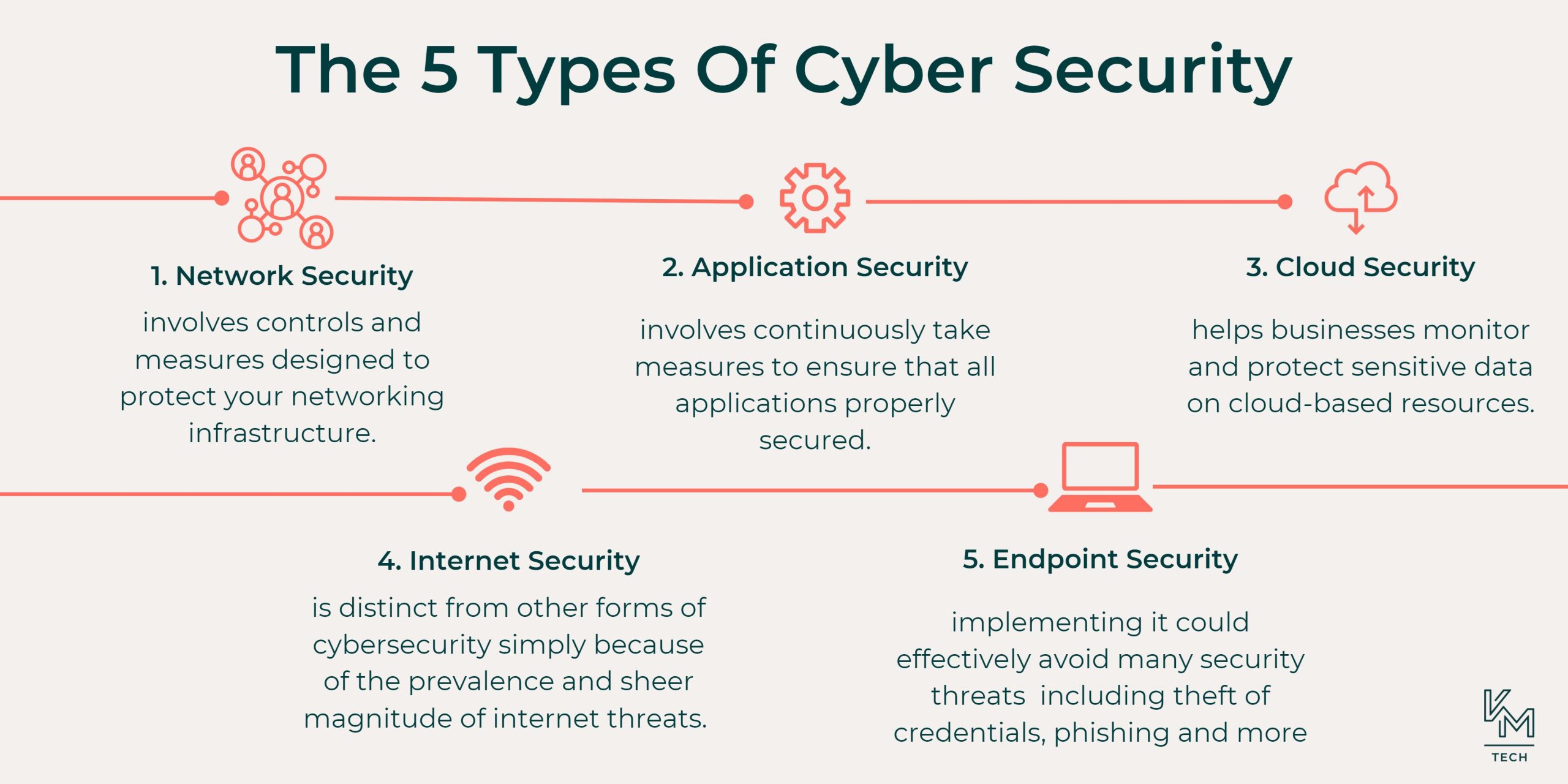
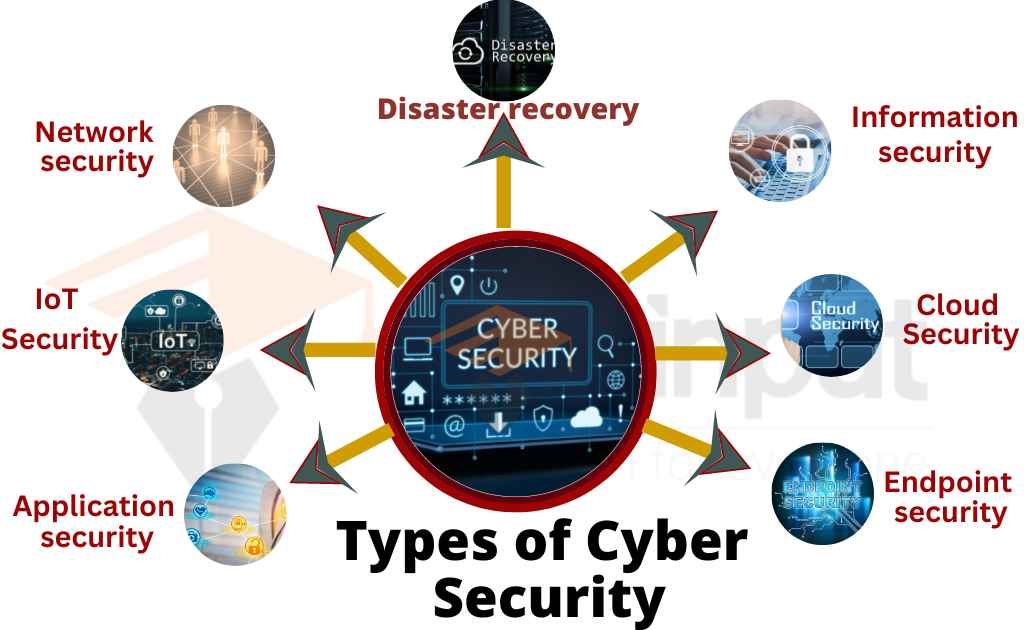
Types Of Cyber Security Coronaforo
What Are The Two Main Types Of Threats To Information Security - [desc-14]